An UBIK® Client establishes a secure connection to the webservice, therefore a certificate has to be provided and installed on the IIS server running UBIK®. If a genuine Root Authority Certificate is already available this can be used. Otherwise, a temporary developer certificate might be used for development and testing.
| In both cases the service itself needs a valid service certificate which refers to the root authority. |
Prerequisites
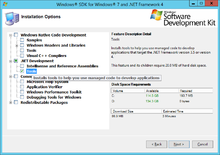
For the creation of development certificates either a visual studio development environment or a .NET framework SDK containing the certification tools is needed. For example, one of these packes can be installed:
- Microsoft Windows SDK for Windows 7 and .NET Framework 4 (Save time and bandwidth by selecting .Net Development Tools, which is sufficient for certification needs)
- Microsoft Visual Studio Express 2013 für Windows Desktop
The binaries for makecert and pvk2pfx can be found here (can vary depending on the used packages):
- C:\Program Files (x86)\Microsoft SDKs\Windows\v7.1A\Bin
- C:\Program Files\Windows Kits\7.1\bin
- C:\Program Files (x86)\Windows Kits\8.1\bin\x64 or .\x86
To use the tools you basically need a windows command console window with admin-rights and the path variable set to the directory contaning the certification binaries. If a visual studio development environment is installed, you alternatively can start a Visual Studio Development Console out of the start menu.
Create Root Authority Certificate
Create a self-signed root authority certificate, which has to be installed on the Client and the Server, using the command
makecert -n "CN=<ROOTNAME>" -r -sv <ROOTNAME>.pvk <ROOTNAME>.cer
where ROOTNAME ... self-signed root authority name (see MSDN).
| This step can be ignored if there is already a valid root authority certificate installed on the server and the client! |
Example: makecert -n "CN=Augmensys" -r -sv AugmensysCA.pvk AugmensysCA.cer
Create Service Certificate
To create a specific service certificate, define the site name (IP) of the service along with the service name.
makecert -sky <SITENAME> -iv <ROOTNAME>.pvk -n "CN=<SITE-IP>" -sv "<SITENAME>.pvk" -ic <ROOTNAME>.cer <SITENAME>.cer -sr currentuser -ss My
where SITENAME ... Name of the service, SITE-IP ... IP of the service (which should be accessed from the client) (see MSDN for details).
Example: makecert -sky AugDemoIIS01 -iv AugmensysCA.pvk -n "CN=137.135.200.180" -sv "AugDemoIIS01.pvk" -ic AugmensysCA.cer AugDemoIIS01.cer -sr currentuser -ss My
Convert Service Certificate for Import in IIS
The created certificate has to be converted prior being imported on an IIS service.
pvk2pfx -pvk "<SITENAME>.pvk" -spc "<SITENAME>.cer" -pfx "<SITENAME>.pfx" -pi <PASSWORD>
(see MSDN for details).
Example: pvk2pfx -pvk "AugDemoIIS01.pvk" -spc "AugDemoIIS01.cer" -pfx "AugDemoIIS01.pfx" -pi mysecretpassword
where PASSWORD ... the user-defined password used for creating the certificate in the previous step.
The certificate is ready to be imported on the IIS now!
Configure IIS
How to configure the IIS using the created certificate(s) can be done as described here.